Corporate Account Takeover is a type of business identity theft in which a criminal entity steals a company’s valid online banking credentials. Small to mid-sized businesses remain the primary target of criminals, but any business can fall victim to these crimes.
Attacks today are typically perpetrated quietly, by the introduction of malware through a simple email or infected website. For businesses that have low resistance to such methods of attack, the malware introduced onto its system may remain undetected for weeks and even months.
Introducing layered security processes and procedures, technological and otherwise, and other tightened security efforts, can help protect businesses from criminals seeking to drain accounts and steal confidential information.
How it’s Done:
Cyber criminals employ various technological and non-technological methods to manipulate or trick victims into divulging personal or account information. Such techniques may include performing an action such as opening an email attachment, accepting a fake friend request on a social networking site, or visiting a legitimate, yet compromised, website that installs malware on their computer(s).
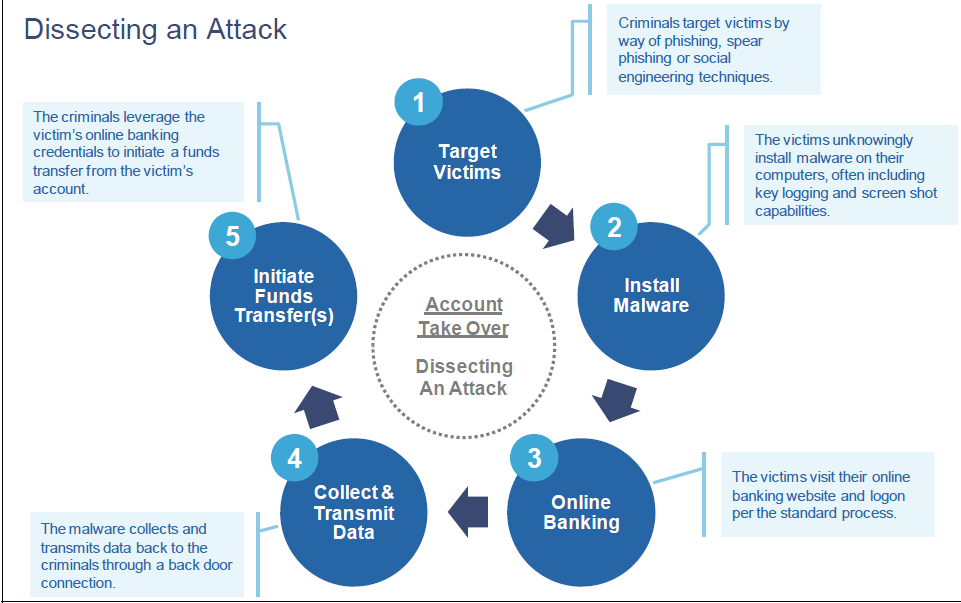
Dissecting an Attack
Cyber criminals will often “phish” for victims using mass emails, pop-up messages that appear on their computers, and/or the use of social networking and internet career sites. For example, cyber criminals often send employees unsolicited emails that:
- Ask for personal or account information;
- Direct the employee to click on a malicious link provided in the email; and/or
- Contain attachments that are infected with malware.
Cyber criminals use various methods to trick employees into opening the attachment or clicking on the link, including:
- Disguising the email to look as though it’s from a legitimate business. Often, these criminals will employ some type of scare tactic to entice the employee to open the email and/or provide account information. For example, cyber criminals have sent emails claiming to be from:
- UPS (e.g., “There has been a problem with your shipment.”)
- Financial institutions (e.g., “There is a problem with your banking account.”)
- Better Business Bureaus (e.g., “A complaint has been filed against you.”)
- Court systems (e.g., “You have been served a subpoena.”)
- Making the email appear to provide information regarding current events such as natural disasters, major sporting events, and celebrity news to entice people to open emails and click on links.
- Using email addresses or other credentials stolen from company websites or victims, such as relatives, co-workers, friends, or executives and designing an email to look like it is from a trusted source to entice people to open emails and click on links.
The cyber criminal’s goal is to get the employee to open the infected attachments or click on the link contained in the email and visit the nefarious website where hidden malware is often downloaded to the employee’s computer. This malware allows the fraudster to “see” and track employee’s activities across the business’ internal network and on the Internet. This tracking may include visits to your financial institution and use of your online banking credentials used to access accounts (account information, log in, and passwords). Using this information, the fraudster can conduct unauthorized transactions that appear to be a legitimate transaction conducted by the company or employee.
How to Protect, Detect, and Respond
Protect
Don’t respond to or open attachments or click on links in unsolicited e-mails. If a message appears to be from your financial institution and requests account information, do not use any of the links provided. Contact the financial institution using the information provided upon account opening to determine if any action is needed. Financial institutions do not:
- Send customers e-mails asking for passwords, credit card numbers, or other sensitive information. Similarly, if you receive an email from an apparent legitimate source (such as the IRS, Better Business Bureau, Federal courts, UPS, etc.) contact the sender directly through other means to verify the authenticity. Be very wary of unsolicited or undesired email messages (also known as “spam”) and the links contained in them.
- Be wary of pop-up messages claiming your machine is infected and offering software to scan and fix the problem, as it could actually be malicious software that allows the fraudster to remotely access and control your computer.
Enhance the security of your computer and networks to protect against this fraud
- Minimize the number of, and restrict the functions for, computer workstations and laptops that are used for online banking and payments. A workstation used for online banking should not be used for general web browsing, e-mailing, and social networking. Conduct online banking and payments activity from at least one dedicated computer that is not used for other online
- Do not leave computers with administrative privileges and/or computers with monetary functions unattended. Log/turn off and lock up computers when not in use.
- Use/install and maintain spam filters.
- Install and maintain real-time anti-virus and anti-spyware desktop firewall and malware detection and removal software. Use these tools regularly to scan your computer. Allow for automatic updates and scheduled scans.
- Install routers and firewalls to prevent unauthorized access to your computer or network. Change the default passwords on all network devices.
- Install security updates to operating systems and all applications, as they become These updates may appear as weekly, monthly, or even daily for zero- day attacks.
- Block pop-ups.
- Keep operating systems, browsers, and all other software and hardware up-to-date.
- Make regular backup copies of system files and work files.
- Do not use public Internet access points (e.g., Internet cafes, public Wi-Fi hotspots (airports), etc.) to access accounts or personal information. If using such an access point, employ a Virtual Private Network (VPN).
Enhance the security of your corporate banking processes and protocols
- Initiate ACH and wire transfer payments under dual control using two separate computers. For example: one person authorizes the creation of the payment file and a second person authorizes the release of the file from a different computer system. This helps ensure that one person does not have the access authority to perform both functions, add additional authority, or create a new user ID.
- If, when logging into your account, you encounter a message that the system is unavailable, contact your financial institution immediately.
Detect
Monitor and reconcile accounts at least once a day
- Reviewing accounts regularly enhances the ability to quickly detect unauthorized activity and allows the business and the financial institution to take action to prevent or minimize losses.
Note any changes in the performance of your computer such as:
- A dramatic loss of speed.
- Changes in the way things appear.
- Computer locks up so the user is unable to perform any functions.
- Unexpected rebooting or restarting of your computer.
- An unexpected request for a one time password (or token) in the middle of an online session.
- Unusual pop-up messages.
- New or unexpected toolbars and/or icons.
- Inability to shut down or restart.
Pay attention to warnings
- Your anti-virus software should alert you to potential viruses. If you receive a warning message, contact your IT professional immediately
Be on the alert for rogue emails
- If someone says they received an email from you that you did not send, you probably have malware on your computer.
- You can also check your email “outbox” to look for email that you did not send
Run regular virus and malware scans of your computer’s hard drive
- This can usually be set to run automatically during non-peak hours.
Respond
If you detect suspicious activity, immediately cease all online activity and:
- Disconnect the Ethernet cable and/or any other network connections (including wireless connections) to isolate the system from the network and prevent any unauthorized access.
- Make sure your employees know how and to whom to report suspicious activity to within your company and at your financial institution
- Immediately contact your financial institution so that the following actions may be taken:
- Disable online access to accounts.
- Change online banking passwords.
- Open new account(s) as appropriate.
- Review all recent transactions and electronic authorizations on the account. If suspicious active transactions are identified, cancel them immediately.
- Ensure that no one has added any new payees, requested an address or phone number change, created any new user accounts, changed access to any existing user accounts, changed existing wire/ACH template profiles, changed PIN numbers or ordered new cards, checks or other account documents be sent to another address
Useful Websites:

